Legal
Data processing Agreement
Feb 13, 2026
This DPA is entered into pursuant to Article 28 of Regulation (EU) 2016/679 (“GDPR”) and applicable African data protection laws (including, where applicable, Nigeria’s data protection legislation, South Africa’s POPIA, Kenya’s Data Protection Act and similar laws in force from time to time) (together, “Data Protection Laws”)
1. Definitions
Unless otherwise defined in the Main Agreement or this DPA, terms have the meaning given in the Data Protection Laws
“Personal Data” means any information relating to an identified or identifiable natural person as defined in Data Protection Laws
“Processing” means any operation performed on Personal Data, whether or not by automated means, as defined in Data Protection Laws
“Data Subject” means an identified or identifiable natural person to whom the Personal Data relates.
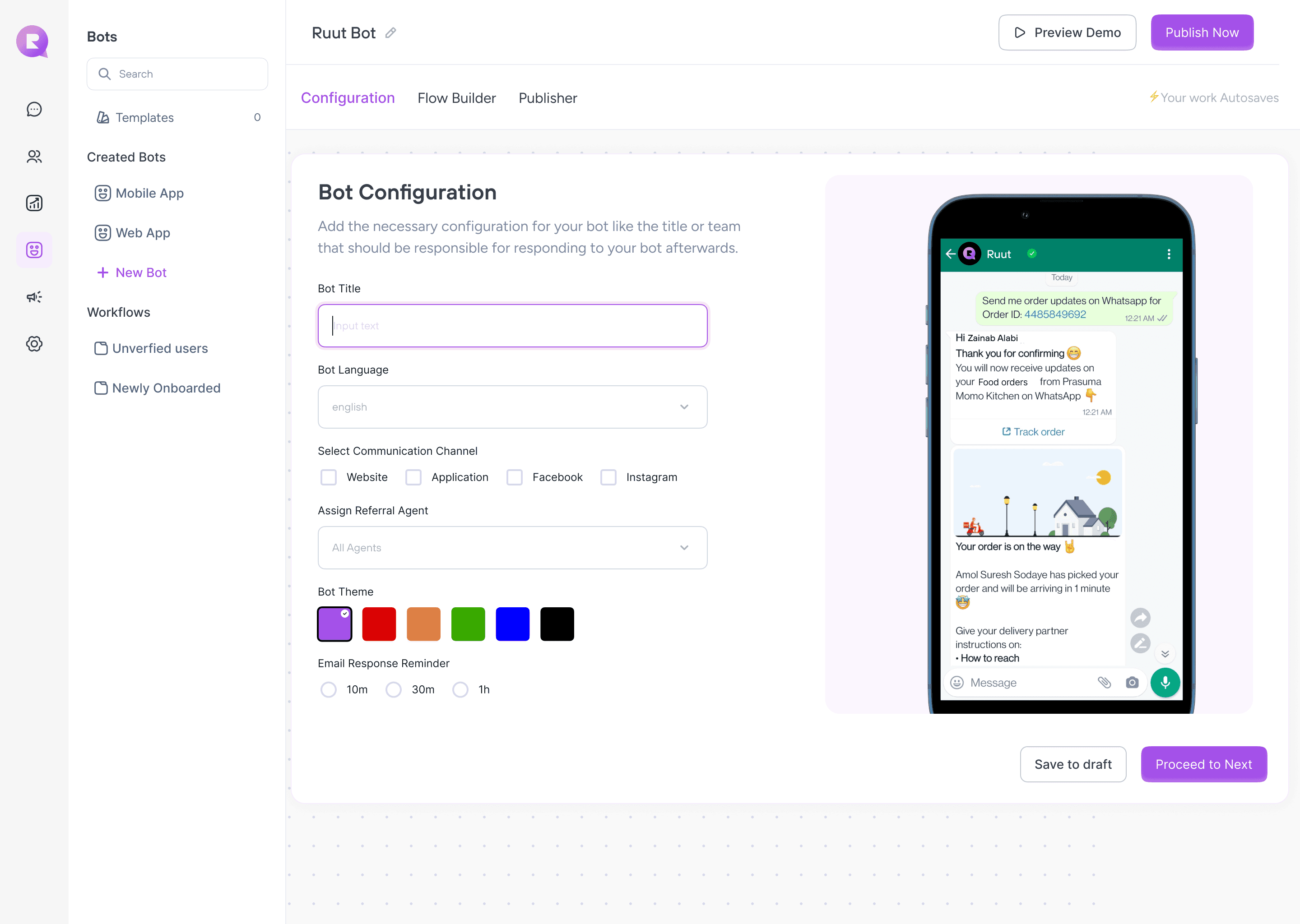
“Services” means the Ruut Chat SaaS platform and related services provided by Processor to Controller under the Main Agreement.
“Sub‑processor” means any third party engaged by a Processor to process Personal Data on behalf of the Controller.
“Personal Data Breach” means a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to, Personal Data transmitted, stored or otherwise processed.
“Data Protection Laws” has the meaning given above and includes any national implementing or supplemental legislation in the EEA, the UK, and relevant African jurisdictions.
2. Roles of the Parties
2.1 Controller determines the purposes and essential means of the Processing of Personal Data.
2.2 Processor processes Personal Data solely on documented instructions from Controller and in accordance with this DPA, the Main Agreement, and applicable Data Protection Laws.
2.3 Processor shall promptly inform Controller if, in its opinion, an instruction infringes Data Protection Laws and may suspend the execution of such instruction until confirmed or modified by Controller
2.4 Processor does not sell Personal Data and does not use Personal Data for its own marketing, profiling, or unrelated analytics purposes. Any use for product improvement is limited to aggregated or anonymised data that no longer constitutes Personal Data.
3. Subject Matter, Duration, Nature and Purpose
3.1 Subject matter. The subject matter of the Processing is the provision of the Services under the Main Agreement.
3.2 Duration. Processing shall commence on the effective date of the Main Agreement and continue for the duration of the Main Agreement, plus any post‑termination period required for return and deletion of Personal Data as set out in Section 12, unless otherwise required by law
3.3 Nature and purpose. Processor processes Personal Data as necessary to:
Enable chat and messaging functionality within the Ruut Chat platform.
Provide user authentication and account management.
Deliver, route, and store messages and conversation history.
Provide customer support and troubleshooting.
Monitor, maintain, secure, and improve the performance and availability of the Services (including abuse prevention, fraud detection, logging, and metrics).
The processor shall not process Personal Data for any purpose other than as expressly documented by the Controller or required by law.
4. Categories of Data Subjects and Personal Data
4.1 Categories of Data Subjects may include:
End users of Ruut Chat as determined by Controller.
Visitors to websites or applications integrated with Ruut Chat.
Employees, contractors, and authorised representatives of the Controller.
4.2 Categories of Personal Data may include (as determined by Controller):
Identification data: name, username, display name, contact details (e.g. email address, phone number).
Usage data: chat messages and conversation content, timestamps, conversation metadata (e.g. participants, channel, status), preferences.
Technical data: IP address, device identifiers, browser and OS information, cookies or similar identifiers, log data.
Account and support data: account configuration, administrative user details, support communications, tickets, audit logs.
4.3 Controller shall not instruct Processor to process special categories of Personal Data or highly sensitive data (e.g. health, biometric, financial account numbers, official identifiers) via the Services unless the Parties have expressly agreed in writing on appropriate safeguards. Processor does not intentionally collect such data.
Controller is responsible for ensuring that its use of the Services and the categories of Personal Data it submits comply with Data Protection Laws and any sector‑specific requirements in Africa or the EU.
5. Processor Obligations
Processor shall, in relation to the Processing of Personal Data on behalf of Controller:
5.1 Process Personal Data only on documented instructions from Controller, including with regard to international transfers, unless required to do so by Union, Member State, or applicable African law; in such case, Processor shall inform Controller of that legal requirement before processing, unless the law prohibits such information.
5.2 Ensure that persons authorised to process Personal Data have committed themselves to confidentiality or are under an appropriate statutory confidentiality obligation.
5.3 Implement appropriate technical and organisational measures to ensure a level of security appropriate to the risk, as described in Section 7 and Annex 1 (Technical and Organisational Measures).
5.4 Assist Controller, taking into account the nature of the processing and the information available to Processor, in ensuring compliance with Controller’s obligations under Data Protection Laws, including Articles 32 to 36 GDPR and similar provisions under African laws (security, breach notifications, data protection impact assessments, and consultations with supervisory authorities).
5.5 Assist Controller, by appropriate technical and organisational measures, in responding to requests from Data Subjects to exercise their rights (see Section 9).
5.6 Notify Controller without undue delay after becoming aware of a Personal Data Breach (see Section 10).
5.7 Make available to Controller all information reasonably necessary to demonstrate compliance with this DPA and Article 28 GDPR, and allow for and contribute to audits and inspections as set out in Section 11.
5.8 Not disclose Personal Data to any third party except as permitted under this DPA, the Main Agreement, or as required by law. Where legally permitted, Processor shall promptly notify Controller of any legally binding request for disclosure by a public authority or law enforcement.
6. Data Retention and Deletion
6.1 Controller‑controlled retention. Controller determines the main retention periods for Personal Data in the Services via its configuration options and policies. Processor shall not actively delete or anonymise Personal Data during the term except in accordance with Controller’s documented instructions, applicable law, or this Section 6.
6.2 Inactivity‑based deletion (optional, configurable). Processor may apply default retention rules for inactive accounts or workspaces (e.g. deletion or anonymisation after a specified period of inactivity), provided that:
Such defaults are transparently described in the Services or documentation.
Controller can request adjusted retention settings in writing where technically feasible.
6.3 Backups. Personal Data may be stored in encrypted backups. Such backups are retained for limited periods for business continuity and disaster recovery and are not restored except where necessary for these purposes. Where feasible, Processor shall ensure that deletion or anonymisation of Personal Data is reflected in backups in line with the backup lifecycle.
6.4 Deletion and return upon termination. Upon termination or expiry of the Main Agreement, Controller may choose to have Personal Data returned or deleted:
Upon written request made within days of termination, Processor shall make available for export a copy of Personal Data in a commonly used machine‑readable format.
Following such export window, Processor shall delete or anonymise Personal Data within [30–60] days, unless Union, Member State, UK or applicable African law requires storage of the Personal Data.
6.5 Processor shall provide written confirmation of deletion or anonymisation upon Controller’s reasonable request.
7. Security Measures
7.1 Processor implements appropriate technical and organisational measures to ensure a level of security appropriate to the risk, taking into account the state of the art, the costs of implementation, and the nature, scope, context and purposes of processing, as well as risks for Data Subjects.
7.2 At a minimum, Processor shall implement the measures described in Annex 1 – Technical and Organisational Measures, which include:
Encryption of data in transit (e.g. TLS) and at rest.
Access control and authentication (role‑based access, least‑privilege, multi‑factor authentication for administrative access).
Logging and monitoring of access and system events.
Network and application security (e.g. firewalls, secure development practices, vulnerability management, penetration testing).
Business continuity and disaster recovery.
Personnel security and training.
7.3 Processor may update its security measures from time to time, provided that such updates do not result in a material reduction in the level of protection for Personal Data.
8. Sub‑processing
8.1 Controller grants Processor a general written authorisation to engage Sub‑processors for hosting, infrastructure, communications, analytics, and operational support necessary to provide the Services.
8.2 Processor shall maintain an up‑to‑date list of Sub‑processors, available upon request or at a public URL notified to Controller. Processor shall notify Controller of any intended addition or replacement of Sub‑processors at least days in advance, thereby giving Controller the opportunity to object on reasonable data protection grounds.
8.3 If Controller reasonably objects to a new Sub‑processor, the Parties shall discuss in good faith to find a commercially reasonable solution. If no such solution is possible, Controller may terminate the affected Services with respect to which the new Sub‑processor is engaged, without penalty, by providing written notice.
8.4 Processor shall impose on each Sub‑processor data protection obligations no less protective than those set out in this DPA by way of a written contract. Processor shall remain fully liable to Controller for the performance of Sub‑processors’ obligations relating to Personal Data.
9. Data Subject Rights
9.1 If Processor receives a request from a Data Subject in relation to Personal Data processed on behalf of Controller (including requests for access, rectification, erasure, restriction, objection, or portability), Processor shall:
Promptly notify Controller of the request.
Not respond directly to the Data Subject except on documented instructions from Controller or where required by law.
9.2 Taking into account the nature of the Processing, Processor shall assist Controller by appropriate technical and organisational measures, insofar as possible, in fulfilling Controller’s obligation to respond to such requests under Chapter III GDPR and comparable provisions in African Data Protection Laws.
9.3 Where Processor is required by law to respond directly to a Data Subject, Processor shall, where legally permitted, inform Controller of such requirement and share a copy of the response.
10. Personal Data Breach Notification
10.1 In the event of a Personal Data Breach affecting Personal Data processed on behalf of Controller, Processor shall notify Controller without undue delay and, where feasible, within [24–48] hours after becoming aware of the breach.
10.2 Such notification shall include at least:
A description of the nature of the Personal Data Breach, including, where possible, the categories and approximate number of Data Subjects concerned and the categories and approximate number of Personal Data records concerned.
The name and contact details of the contact point where more information can be obtained.
The likely consequences of the Personal Data Breach.
The measures taken or proposed to be taken by Processor to address the Personal Data Breach, including measures to mitigate its possible adverse effects.
10.3 Processor shall promptly take reasonable steps to investigate, mitigate, and remedy the Personal Data Breach and co‑operate with Controller and any supervisory authorities as required.
11. Audits and Compliance
11.1 Processor shall make available to Controller all information reasonably necessary to demonstrate compliance with this DPA and Article 28 GDPR and applicable African Data Protection Laws.
11.2 Upon at least days’ prior written notice (save where a shorter period is required by a supervisory authority or due to an actual or suspected Personal Data Breach), Controller or an independent auditor mandated by Controller may conduct an audit, including inspections, of Processor’s relevant data processing facilities and practices no more than once per months.
11.3 Processor may satisfy audit requests by providing up‑to‑date attestations, certifications, or summaries of audit reports (e.g. ISO 27001, SOC 2 or equivalent) that demonstrate the effectiveness of its technical and organisational measures. On‑site audits shall:
Occur during normal business hours.
Not unreasonably interfere with Processor’s operations.
Be subject to confidentiality obligations and security restrictions.
Be at Controller’s expense; Processor may charge a reasonable fee for its support where permitted by law.
12. Data Return and Deletion upon Termination
12.1 Upon termination or expiry of the Main Agreement, Controller may, by written request within days:
Request a copy of Personal Data in a commonly used machine‑readable format; and/or
Instruct Processor to delete and/or anonymise Personal Data.
12.2 Unless otherwise required by law, Processor shall, at Controller’s choice, delete or anonymise all Personal Data (and delete existing copies) within [30–60] days after the export window described in Section 12.1.
12.3 Where Union, Member State, UK or applicable African law requires retention, Processor shall retain Personal Data only for as long as such law requires and shall ensure that such Personal Data is processed only for the purposes mandated by that law.
13. International Data Transfers
13.1 Processor shall not transfer Personal Data outside the EEA, the UK, or the African country of origin (where local law restricts cross‑border transfers) unless such transfer complies with Chapter V GDPR and any analogous provisions under applicable African Data Protection Laws (e.g. NDPR, POPIA, Kenya DPA cross‑border rules).
13.2 Where Personal Data is transferred to a country that does not benefit from an adequacy decision, Processor shall ensure that appropriate safeguards are in place, such as:
Standard Contractual Clauses (SCCs) adopted by the European Commission for transfers to third countries (including Module 2 / Module 3 as applicable).
Other lawful transfer mechanisms recognised under Data Protection Laws, plus any supplementary measures that may be required.
13.3 Where SCCs apply, the Parties agree that such clauses are incorporated by reference into this DPA and will execute any additional documents necessary to give them full effect.
13.4 Where African laws require specific contractual clauses or approval from supervisory authorities for cross‑border transfers, the Parties shall co‑operate in good faith to implement such mechanisms (e.g. contractual clauses, approvals) as necessary.
14. Liability and Priority
14.1 The Parties’ respective liability under or in connection with this DPA shall be governed by the liability provisions in the Main Agreement, subject to any mandatory provisions of Data Protection Laws.
14.2 Nothing in this DPA shall limit either Party’s liability towards Data Subjects under Data Protection Laws.
14.3 In the event of any conflict or inconsistency between this DPA and the Main Agreement in relation to data protection and privacy, this DPA shall prevail to the extent of such conflict.
15. Governing Law and Jurisdiction
15.1 This DPA shall be governed by and construed in accordance with the laws of [Choose an EU Member State, e.g. Ireland / Netherlands / Germany], without regard to conflict of laws rules, to the extent that such choice is compatible with Data Protection Laws
15.2 Any disputes arising from or in connection with this DPA shall be subject to the exclusive jurisdiction of the courts of [same Member State], without prejudice to the rights of Data Subjects or supervisory authorities under Data Protection Laws.
Annex 1 – Technical and Organisational Measures (TOMs)
The following is a non‑exhaustive description of the security measures implemented by Processor for the Ruut Chat Services:
Organisation of Information Security
Information security policy approved by management and reviewed regularly.
Defined roles and responsibilities for security and privacy.
Access Control
Unique user IDs for staff, strict role‑based access control, least‑privilege principle.
Multi‑factor authentication for administrative and production access.
Regular review of access rights and timely removal of access on role change or termination.
Encryption
Data in transit is protected with strong encryption (e.g. TLS 1.2+).
Data at rest encrypted using industry‑standard algorithms (e.g. AES‑256).
Physical and Environmental Security
Use of reputable data centre / cloud providers with robust physical security controls (e.g. access controls, CCTV, visitor logs).
Operations and System Security
Secure configuration baselines for servers, databases, and applications.
Vulnerability management, including regular patching and vulnerability scanning.
Change management procedures for deployments.
Application Security
Secure development lifecycle with code review and secure coding standards.
Regular internal and/or external penetration testing.
Logging and Monitoring
Logging of access and significant system events.
Monitoring and alerting for suspicious activity, availability issues, and security events.
Business Continuity and Disaster Recovery
Regular backups of key systems and data, stored securely.
Documented incident response and disaster recovery plans, with periodic testing.
Staff Training and Confidentiality
Security and privacy awareness training for employees with access to Personal Data.
Confidentiality obligations in employment and contractor agreements.
Data Protection by Design and Default
Minimisation of Personal Data processed and stored.
Configurable privacy and security options for Controllers within the Services, where feasible.
Questions
Find answers to common questions about our platform
Can i pay in my local currency
Is my data secure with Ruut?
Do you have a free trial
What happens to my data if I cancel my subscription?
Can I customize the Ruut interface to fit my needs??